The effectiveness of spearphishing, the use of highly targeted email to compromise systems and data, depends upon the miscreant’s ability to craft an email that is enticing to the recipient. This presents the phisher with two problems — identifying the target and determining what would entice the target.
After years of clandestine efforts, secret operatives of the United States were able to kill bin Laden. Running this operation was a CIA employee whose identity is a closely guarded national secret. The Observer reports that his cover was blown using Flickr. The White House published a photo from the Situation Room which, although it did now show the CIA employee’s face, did show his yellow tie. Also, it appeared that he was tall. This photo allowed John Young of Cryptome.org, an intelligence blog dedicated to exposing government secrets, to get started. The White House posted several other photos from that day and the using the clues of the necktie and height, Young was able to find a photo of the man’s face. Within a day, Young was able to determine the CIA employee’s name, where he went to school, his college GPA, where he lived, the sports his kids played and his wife’s activities. The Observer dubbed him “CIA John” to protect his identity. This is CIA John.
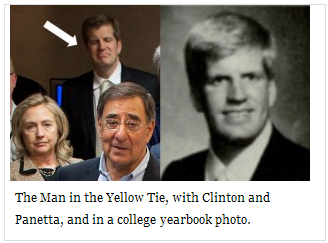
Armed with this data, a spearphishing attack could be mounted against CIA John.
What if the spearphisher doesn’t have White House photographs to find the victims? Finding targets is as easy as taking pictures of employees in the parking lot. Carnegie Mellon University researchers led by Alessandro Acquisti took photographs of student volunteers. Using facial recognition software on social networking sites, the researchers were able to identify 31% of the students by name. In another experiment, the Carnegie Mellon team was able to identify 10% of people who had posted their photos on public dating sites. The researcher’s have posted their research online, Faces of Facebook: Privacy in the Age of Augmented Reality. The researchers report that they have been able to use profile photos and facial-recognition software to get details such as birthdate and social security number predictions.
Social media provides a powerful source of data for spearphishers to identify and and target individuals.
